Helping you start, manage, and protect your business within your budget
We Are Problem Solvers
- Need help protecting your business idea?
- Want to know what legal structure is best for your business?
- Have issues with your trademark application?
- Need help responding to a letter from another attorney?
- Have problems with your business partner?
- Want help selling, buying, or investing in a business?
- Have contracts that need to be changed or don’t understand?
- Need help enforcing a contract?
- Have questions about how to start your business?
- Need help understanding what licenses you need for your business?
Legal Services for Small and Medium Size Businesses
Start Your Business
Corporation Formation
Partnership Formation
Operating Agreement
Bylaws
Licenses and permits
Manage Your Business
Commercial Contracts
Business transactions
Terms of Use
Data Compliance
Regulatory advice
IP License Agreements
Protect your Business
Trademarks Registration
Copyright Registration
Non-Disclosure Agreements
Non-Compete Agreements
Preliminary patents assessments
Cease and desist letters
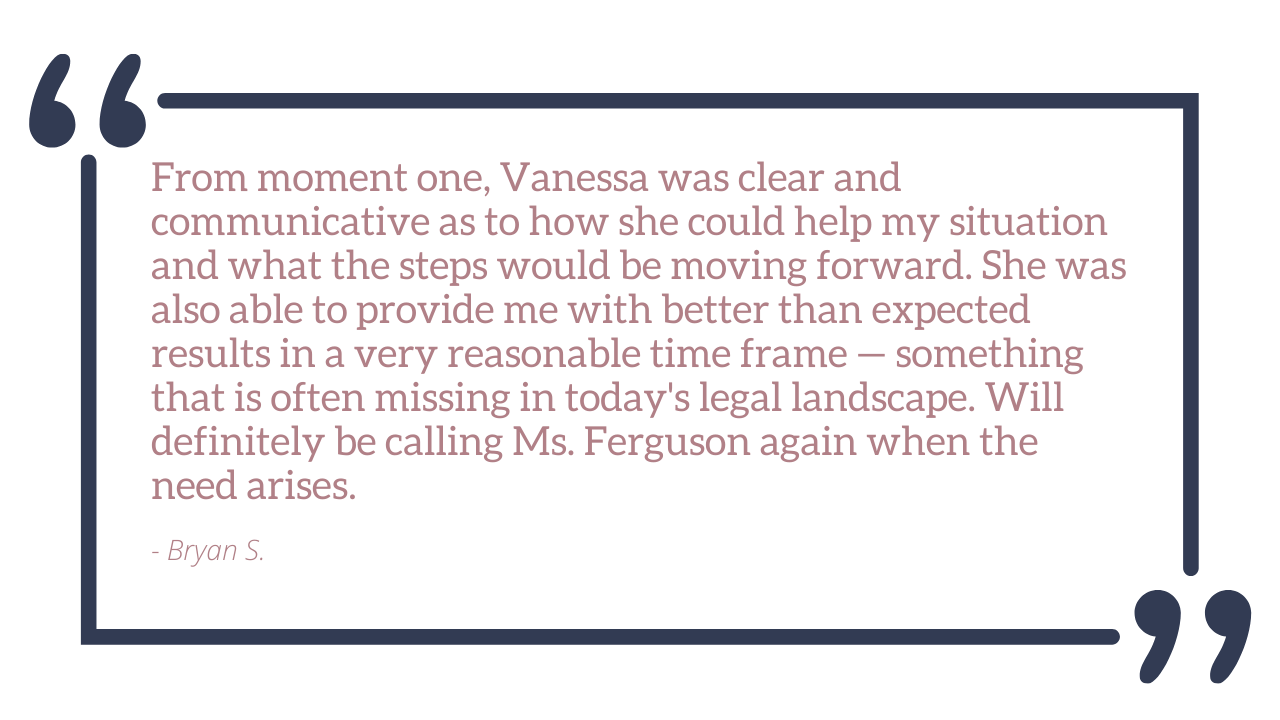
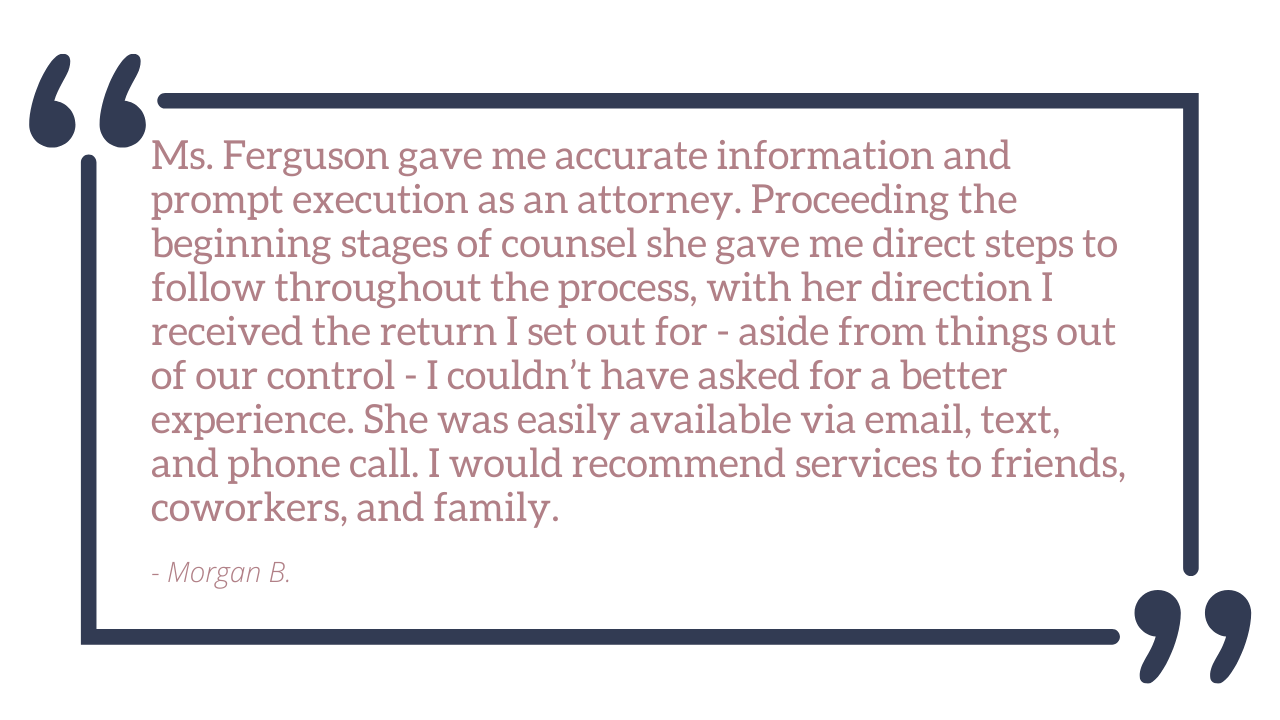
At Ferguson Legal, PLLC, we help innovative businesses address their legal needs effectively. At Ferguson Legal, PLLC, we focus on business transactions including contract drafting, negotiations, and reviews.
In addition to general business matters, we also advise businesses on how to protect their intellectual property and limit their exposure to Data Privacy violations. On the intellectual property side, we provide innovative businesses with legal assistance related to trademarks, copyrights, and trade Secrets. Our assistance includes IP registration, IP disputes, trademark office actions, licensing agreements, IP assignments, and more. On the data privacy side, we help technology-based businesses develop data privacy compliance software, programs, platforms, applications, and websites.
We also offer monthly subscription services that start as low as $79.99 /month.
A successful entrepreneur has an innovative lawyer on their team – never take the journey alone.